Answer:
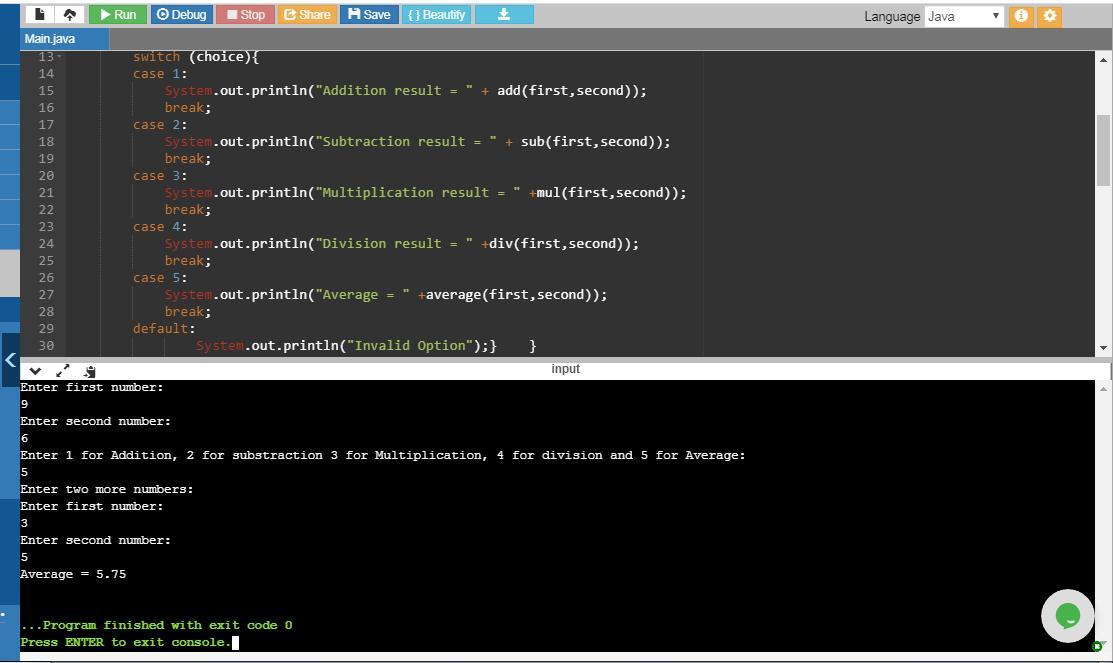
Here is the JAVA program:
import java.util.Scanner;
public class Operations{
public static void main(String[] args) {
Scanner input= new Scanner(System.in);
float first,second;
System.out.println("Enter first number:");
first = input.nextFloat();
System.out.println("Enter second number:");
second = input.nextFloat();
System.out.println("Enter 1 for Addition, 2 for Subtraction 3 for Multiplication, 4 for Division and 5 for Average:");
int choice;
choice = input.nextInt();
switch (choice){
case 1: //calls add method to perform addition
System.out.println("Addition result = " + add(first,second));
break;
case 2: //calls sub method to perform subtraction
System.out.println("Subtraction result = " + sub(first,second));
break;
case 3: //calls mul method to perform multiplication
System.out.println("Multiplication result = " +mul(first,second));
break;
case 4: //calls div method to perform division
System.out.println("Division result = " +div(first,second));
break;
case 5: //calls average method to compute average
System.out.println("Average = " +average(first,second));
break;
default: //if user enters anything other than the provided options
System.out.println("Invalid Option"); }}
public static float add(float first, float second) {
float result = first + second;
if(result<0)
{System.out.println("Oops option 1 is returning a negative number that is: "); }
return result; }
public static float sub(float first, float second) {
float result = first - second;
if(result<0){System.out.println("Oops option 2 is returning negative number that is: ");}
return result; }
public static float mul(float first, float second) {
float result = first*second;
if(result<0)
{System.out.println("Oops option 3 is returning negative number that is: ");}
return result; }
public static float div(float first, float second){
if(second==0)
{System.out.println("Division by 0");}
float result = first/second;
if(result<0){System.out.println("Oops option 4 is returning negative number that is: ");}
return result; }
public static float average (float first,float second) {
Scanner inp= new Scanner(System.in);
float first2,second2;
System.out.println("Enter two more numbers:");
System.out.println("Enter first number:");
first2 = inp.nextInt();
System.out.println("Enter second number:");
second2 = inp.nextInt();
float result;
float sum = first+second+first2+second2;
result = sum/4;
if(result<0)
{System.out.println("Oops option 5 is returning negative number that is: ");}
return result; }}
Explanation:
The above program first prompts the user to enter two numbers. Here the data type of two number is float in order to accept floating numbers. The switch statement contains cases which execute according to the choice of user. The choice available to user is: 1,2,3,4 and 5
If the user selects 1 then the case 1 executes which calls the method add. The method add takes two numbers as parameters, adds the two numbers and returns the result of the addition. This result is displayed on output screen. However if the result of addition is a negative number then the message: "Oops option 1 is returning the negative number that is:" is displayed on the screen along with the negative answer of that addition.
If the user selects 2 then the case 2 executes which calls the method sub. The method works same as add but instead of addition, sub method takes two numbers as parameters, subtracts them and returns the result of the subtraction.
If the user selects 3 then the case 3 executes which calls the method mul. The method mul takes two numbers as parameters, multiplies them and returns the result of the multiplication.
If the user selects 4 then the case 4 executes which calls the method div. The method div takes two numbers as parameters and checks if the denominator i.e. second number is 0. If its 0 then Division by 0 message is displayed along with result i.e. infinity. If second number is not 0 then method divides the numbers and returns the result of the division.
If the user selects 5 then the case 5 executes which calls the method average. The average method then asks the user to enter two more numbers first2 and second2 and takes the sum of all four numbers i.e. first, second, first2 and second2. Then the result of sum is divided by 4 to compute average. The method returns the average of these four numbers.